Here are the key takeaways from the blog:
- Advanced techniques streamline IT risk assessments: The firm's innovative approach reduces client effort, improves data collection, and enhances assessment results.
- Financial risk measurement is critical: Moving beyond “high/medium/low” scales to dollar-based risk quantification improves decision-making and aligns better with executive expectations.
- Continuous updates and automation boost effectiveness: Integrating risk assessment checkpoints into change management and procurement processes ensures assessments stay relevant and audit-ready.
- Tailored, real-time IT risk assessments: Rivials' platform offers quantified risk assessments, delivering proactive insights and innovative reporting to help organizations manage risks efficiently and align with evolving cybersecurity needs
Examiner Approved Cyber Risk Model
Check out the Cyber Risk Management Model that examiners reference


Part of our mission at Rivial Data Security is to constantly innovate and look for better ways to add value for our clients. We use several advanced techniques in our IT Risk Assessment solution that reduce the amount of effort required of our clients, streamline the process of collecting risk information, and improve the risk assessment results.
You can learn the fundamentals of conducting an IT risk assessment in our blog, “Complete Guide to IT Risk Assessments”. However, if you’re looking for advanced IT risk assessment techniques, keep reading!
Information Assets
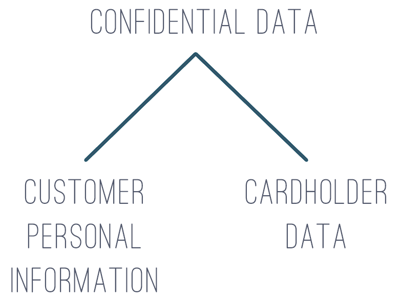
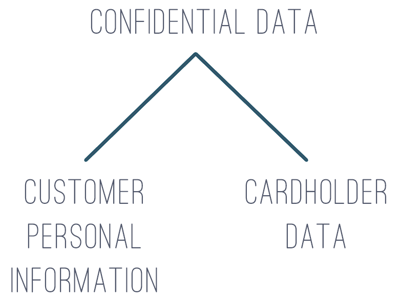
Early in the risk assessment process, we recommend identifying the types of information being stored and transmitted by your information systems. It is possible to use your existing data classification structure (e.g. public data, internal use only, confidential) but we recommend going a bit beyond the traditional three tiers and breaking out different types of information. For example: you can break confidential data into customer personal information and cardholder data to help your PCI scoping efforts.
Information Systems
If you use an asset-based approach, you will want to identify information systems such as major business applications and supporting infrastructure. Two criteria we use to help identify information systems are:
- a single person or team is responsible for the group of technology devices
- the security controls are similar
For example, if you outsource your core banking application, the vendor is responsible for the database backend, the web application frontend, and the infrastructure tying the two together. That is an information system. As another example, all Windows Servers in your environment could be lumped together into one information system because one team typically supports them (IT) and they are all secured similarly.
Financial Measures
The truth is, we as an industry don’t measure IT risk well and we’re still in the wild west of information security decision-making. Most risk gets measured and communicated using an ordinal scale, or a measurement that denotes an order. For example, medium is higher than low, and high is higher than medium. Two is more than one, neutral is better than bad. As an industry, we cybersecurity people typically report risk as high, medium, and low. We expect our business leaders to spend real dollars on security solutions. But we don’t give them a real explanation of the benefits. There are several techniques available for measuring IT risk in financial terms, the sooner you stop reporting risk in ordinal scales and start reporting risk in financial terms, the happier your executives will be. To learn more about the imperative of reporting risk in financial terms, check out our blog “Quantitative vs Qualitative Risk Assessments”.
We also recommend the book How to Measure Anything in Cybersecurity Risk by Douglas W. Hubbard and Richard Seiersen for additional measuring techniques.
Loss Tolerance
Sometimes referred to as risk appetite or risk tolerance, the loss tolerance of the organization’s leadership is a critical part of ongoing risk management. If you are measuring IT risk in financial terms, as mentioned above, you are one step closer to defining a loss tolerance with meaning and substance. By asking a handful of questions about the probability of certain loss amounts, a group of executives or Board members can quickly pinpoint their overall appetite for risk. The risk tolerance can be charted on a scale and compared to actual risk measures for better decision-making.
Ongoing Updates
IT risk assessment—like any decision tool—needs to be updated regularly in order to be useful. As things change in the environment, those changes need to be reflected in the IT Risk Assessment, which can be done in a variety of ways. One trick we use is adding a line in the change management process that requires an IT risk assessment triage step. Another trick is adding a similar line to the organization’s procurement process. Any new purchases should go through the IT risk management team/person so the risk assessment can be updated accordingly. I strongly recommend setting up automated monthly reminders for system owners and admins to ensure continuous updates and demonstrate compliance during regulatory audits. Many regulatory bodies, such as NIST, FDIC, and NCUA, have emphasized that automation and ongoing updates is a key components in enhancing cybersecurity programs, particularly as regulatory requirements around technology continue to grow.

Key Performance Indicators
The next evolution beyond regular updates is gathering real-time, or near real-time, data around the risk assessment details. Particularly around the performance of security controls. In many technology environments measurements can be configured, and automated, to feed information into the risk assessment. Known as Key Performance Indicators (KPIs), these metrics provide insight into the effectiveness of security measures, allowing organizations to monitor performance against set thresholds and quickly identify any areas of concern. By comparing these KPIs to established thresholds, organizations can proactively adjust risk levels and take corrective action when certain metrics signal heightened risk.
Compliance Integration
The name of the game in any organization is efficiency. Therefore, any time you can remove duplication of effort, the organization wins. Considering the significant overlap between IT risk management controls and IT compliance controls (note: they don’t perfectly align because security does not equal compliance and visa versa) there is ample opportunity to automatically adjust risk measures and compliance measures as control details are gathered, whether through testing or key performance indicator reporting. For example, if an antivirus metric falls below a desired threshold, both the related risk measurement and the related compliance measurement are impacted negatively. Updating both at the same time is more accurate and saves time.
Try Rivals Risk Assessment
IT risk assessments are incredibly useful tools to help executives and Board Members make decisions, but not all financial institutions have the robust resources to successfully execute and utilize their assessments in-house. Our team knows how to deliver cutting-edge solutions for all budgets and sizes. If you’re looking for an easier way to accomplish your IT risk assessment, talk to one of our consultants and take advantage of our time-saving modifications and innovative reporting capabilities.
Not only do we offer comprehensive one-time IT risk assessments tailored to identify your organization's immediate risks, but our platform excels in providing real-time risk management. With our advanced tool, you gain continuous monitoring and proactive insights to address potential threats as they emerge. This ensures your security strategies remain aligned with the ever-evolving cyber landscape, reducing downtime and safeguarding critical assets. Let us show you how we can transform your approach to IT risk management—schedule a call today and experience the power of a dynamic security solution in action.
Examiner Approved Cyber Risk Model
Check out the Cyber Risk Management Model that examiners reference




 Randy Lindberg
Randy Lindberg